Multi-Factor Authentication (MFA)
Overview
Multi-Factor Authentication (MFA) adds an extra layer of security by requiring users to provide two or more verification factors to access AWS resources. MFA combines something you know (password) with something you have (MFA device) or something you are (biometrics).
As of 2025, AWS has made MFA mandatory for all root users across all account types. This enforcement prevents over 99% of password-related attacks. Understanding MFA types, implementation, and policy enforcement is essential for the SAA-C03 exam.
2025 MFA Requirement
AWS now requires MFA for all root users. Starting Spring 2025, all AWS Organizations member account root users must register MFA within 35 days of first sign-in to access the AWS Management Console.
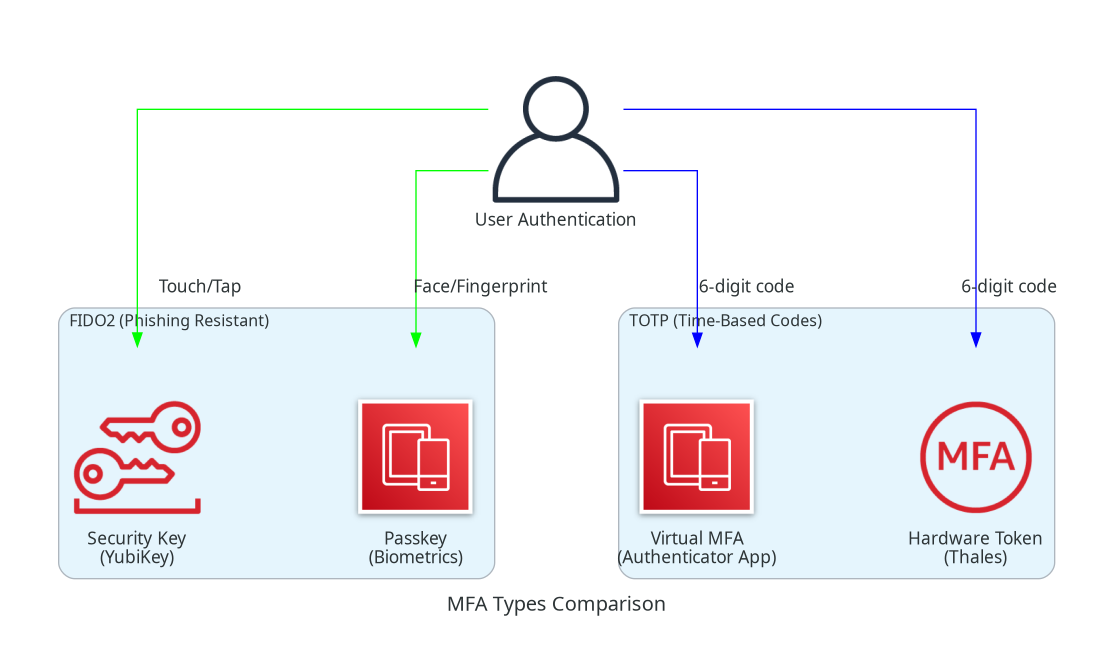
Know the difference between FIDO2/passkeys (phishing-resistant) and TOTP tokens (time-based codes). Exam questions often ask which MFA type provides the strongest security.
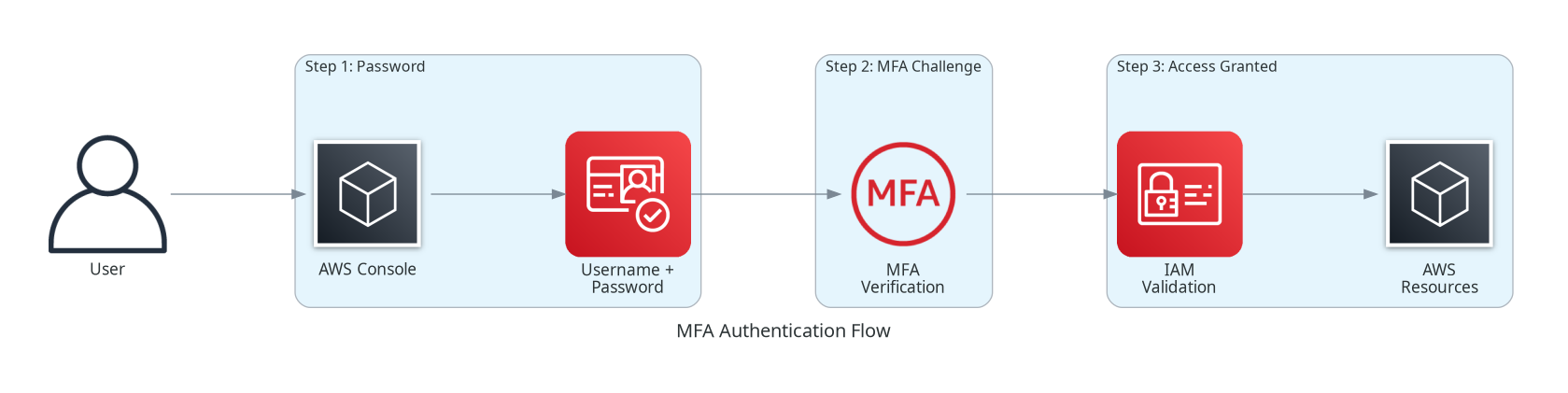
Architecture Diagram
Key Concepts
MFA Device Types
AWS supports three main types of MFA devices:
Passkeys & Security Keys (FIDO2)
FIDO2-based authentication provides the strongest, phishing-resistant MFA:
Security Keys (Hardware):
- Physical devices like YubiKey that connect via USB, NFC, or Bluetooth
- No batteries required
- A single key can protect multiple AWS accounts
- Based on public key cryptography
Synced Passkeys (Software):
- Cloud-based credentials synced across devices
- Providers: iCloud Keychain, Google Password Manager, 1Password, Dashlane
- Use biometrics (fingerprint, face) or device PIN
- Phishing-resistant like hardware keys
Benefits:
- Strongest protection against phishing attacks
- No codes to type - just touch or biometric scan
- Can be used across multiple accounts
Virtual MFA Devices (TOTP)
Virtual MFA applications generate time-based one-time passwords (TOTP):
How It Works:
- App generates 6-digit codes that change every 30 seconds
- Based on RFC 6238 TOTP algorithm
- Requires time synchronization between device and AWS
Popular Apps:
- Google Authenticator
- Microsoft Authenticator
- Authy
- Duo Mobile
Characteristics:
- Free and easy to set up
- Single app can store tokens for multiple accounts
- Codes must be entered manually
Hardware TOTP Tokens
Physical hardware tokens generate time-based codes:
Characteristics:
- Dedicated physical device (e.g., Thales tokens)
- Pre-shared seed from AWS-approved sources only
- Display 6-digit codes like virtual MFA
- Battery-powered (limited lifespan)
When to Use:
- High-security environments
- Compliance requirements mandating hardware tokens
- Air-gapped or no-phone environments
Note: AWS recommends security keys over hardware TOTP tokens due to better usability and no battery requirements.
MFA Device Comparison
| Feature | FIDO2 Security Key | Passkey (Synced) | Virtual MFA App | Hardware TOTP |
|---|---|---|---|---|
| Phishing Resistant | Yes | Yes | No | No |
| Battery Required | No | No (device battery) | No (device battery) | Yes |
| Cost | $20-50 | Free | Free | $15-30 |
| Multiple Accounts | Yes | Yes | Yes (in app) | No (1 per device) |
| Backup Method | Second key | Cloud sync | Recovery codes | Manual backup |
| Best For | High security | Convenience + security | General use | Compliance |
MFA Policy Enforcement
Enforcing MFA with IAM Policies
You can require MFA for specific actions using IAM policy conditions:
Condition Key: aws:MultiFactorAuthPresent
true- Request was authenticated with MFAfalse- Request was NOT authenticated with MFA
Condition Key: aws:MultiFactorAuthAge
- Checks how many seconds since MFA authentication
- Useful for requiring recent MFA for sensitive operations
How It Works
MFA Authentication Flow
Step 1: Initial Authentication
User provides username and password (first factor).
Step 2: MFA Challenge
AWS prompts for the second factor based on configured MFA device type.
Step 3: MFA Verification
| MFA Type | User Action | Verification |
|---|---|---|
| Security Key | Touch device | Cryptographic signature |
| Passkey | Biometric/PIN | Cryptographic signature |
| Virtual MFA | Enter 6-digit code | TOTP validation |
| Hardware TOTP | Enter 6-digit code | TOTP validation |
Step 4: Access Granted
Upon successful verification, user gains access to AWS resources.
Implementing MFA
Enabling MFA for Root User
Root User MFA - Critical Priority
Always enable MFA on root user first! The root user has unrestricted access that cannot be limited by IAM policies. Use the strongest MFA available (FIDO2 security key or passkey).
Enabling MFA for IAM Users
- Navigate to IAM Console > Users
- Select user > Security credentials tab
- Click "Assign MFA device"
- Choose device type and follow setup wizard
MFA Device Limits
MFA Device Limits
| Account Type | Max MFA Devices | Notes |
|---|---|---|
| Root User | 8 devices | Can mix different MFA types |
| IAM User | 8 devices | Can mix different MFA types |
| Per Device | 1 user only | Cannot share devices between users |
Requiring MFA for Sensitive Operations
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "DenyAllExceptListedWithoutMFA",
"Effect": "Deny",
"NotAction": [
"iam:CreateVirtualMFADevice",
"iam:EnableMFADevice",
"iam:GetUser",
"iam:ListMFADevices",
"iam:ListVirtualMFADevices",
"iam:ResyncMFADevice",
"sts:GetSessionToken"
],
"Resource": "*",
"Condition": {
"BoolIfExists": {
"aws:MultiFactorAuthPresent": "false"
}
}
}
]
}{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "RequireRecentMFA",
"Effect": "Deny",
"Action": [
"ec2:StopInstances",
"ec2:TerminateInstances",
"rds:DeleteDBInstance"
],
"Resource": "*",
"Condition": {
"NumericGreaterThan": {
"aws:MultiFactorAuthAge": "3600"
}
}
}
]
}MFA with AWS CLI
To use MFA with AWS CLI, you must request temporary credentials:
# Get temporary credentials with MFA
aws sts get-session-token \
--serial-number arn:aws:iam::123456789012:mfa/user-name \
--token-code 123456
# Response contains temporary credentials:
# {
# "Credentials": {
# "AccessKeyId": "ASIA...",
# "SecretAccessKey": "...",
# "SessionToken": "...",
# "Expiration": "2024-01-15T12:00:00Z"
# }
# }
# Export credentials for subsequent commands
export AWS_ACCESS_KEY_ID=ASIA...
export AWS_SECRET_ACCESS_KEY=...
export AWS_SESSION_TOKEN=...Best Practices
MFA Best Practices
- Use FIDO2/Passkeys When Possible - Phishing-resistant, strongest protection
- Enable Multiple MFA Devices - Register backup devices for redundancy
- Require MFA for All Users - Especially console access and sensitive operations
- Use Hardware Security Keys for Root - Physical possession required
- Store Backup Devices Securely - Keep spare MFA device in a safe/vault
- Monitor MFA Status - Use AWS Config rules to check MFA compliance
Recovery Planning
MFA Recovery Options
| Scenario | Recovery Method |
|---|---|
| Lost virtual MFA device | Use backup MFA device or contact AWS Support |
| Lost security key | Use backup security key or passkey |
| All MFA devices lost (IAM user) | Admin can deactivate MFA and allow re-enrollment |
| All MFA devices lost (root user) | AWS Support identity verification process |
Common Exam Scenarios
MFA Exam Scenarios
| Scenario | Solution | Why |
|---|---|---|
| Company wants phishing-resistant MFA for executives | FIDO2 security keys or passkeys | Cryptographic authentication cannot be phished |
| Users complain MFA is inconvenient | Synced passkeys with biometrics | One-touch authentication, synced across devices |
| Require MFA only for production account access | IAM policy with aws:MultiFactorAuthPresent condition | Enforces MFA at policy level |
| User lost their MFA device | Admin deactivates MFA, user re-enrolls with new device | IAM admins can manage user MFA devices |
| Need MFA for CLI/API access | Use sts:GetSessionToken with MFA code | CLI requires temporary credentials for MFA |
| Compliance requires hardware MFA tokens | Hardware TOTP tokens from AWS-approved vendor | Physical token meets compliance requirements |
Common Pitfalls
Pitfall 1: Not Enabling MFA on Root Account
Mistake: Leaving the root account without MFA protection.
Why it's dangerous:
- Root account has unlimited, unrestricted access
- Cannot be limited by any IAM policy
- Single point of failure for entire AWS account
Correct Approach:
- Enable MFA on root account immediately after account creation
- Use strongest MFA available (FIDO2 security key)
- Store backup MFA device in secure location
Pitfall 2: Single MFA Device with No Backup
Mistake: Registering only one MFA device without backup.
Why it's dangerous:
- Lost/broken device = locked out of account
- Recovery process can take days
- Business continuity risk
Correct Approach:
- Register at least 2 MFA devices
- Store backup device in separate secure location
- For passkeys, ensure they're synced to cloud backup
Pitfall 3: Confusing MFA Types for CLI
Mistake: Assuming FIDO2 security keys work directly with AWS CLI.
Why it fails:
- FIDO2/Passkeys only work with AWS Management Console
- CLI and API require TOTP-based MFA with sts:GetSessionToken
Correct Approach:
- Use virtual MFA for CLI access
- Call GetSessionToken with MFA code to get temporary credentials
- Use those temporary credentials for CLI commands
Pitfall 4: Not Enforcing MFA via Policy
Mistake: Enabling MFA for users but not requiring it in policies.
Why it matters:
- Users might bypass MFA using access keys directly
- Programmatic access can bypass MFA requirement
- Inconsistent security posture
Correct Approach:
- Create IAM policies that deny actions without MFA
- Use conditions like
aws:MultiFactorAuthPresent - Apply to sensitive operations at minimum
Test Your Knowledge
Which MFA type provides phishing-resistant authentication?
How many MFA devices can be registered per IAM user?
A user needs to use MFA with AWS CLI. What must they do?
Which IAM condition key checks if MFA was used?
Related Services
Quick Reference
MFA Condition Keys
aws:MultiFactorAuthPresent - Boolean: true if MFA was used
aws:MultiFactorAuthAge - Numeric: seconds since MFA authenticationCLI Commands for MFA Management
# List MFA devices for current user
aws iam list-mfa-devices
# List all virtual MFA devices in account
aws iam list-virtual-mfa-devices
# Create virtual MFA device
aws iam create-virtual-mfa-device --virtual-mfa-device-name MyMFADevice
# Enable MFA device for user
aws iam enable-mfa-device \
--user-name username \
--serial-number arn:aws:iam::123456789012:mfa/MyMFADevice \
--authentication-code1 123456 \
--authentication-code2 789012
# Deactivate MFA device
aws iam deactivate-mfa-device \
--user-name username \
--serial-number arn:aws:iam::123456789012:mfa/MyMFADevice
# Get session token with MFA
aws sts get-session-token \
--serial-number arn:aws:iam::123456789012:mfa/username \
--token-code 123456MFA ARN Formats
Virtual MFA: arn:aws:iam::ACCOUNT-ID:mfa/DEVICE-NAME
Hardware: arn:aws:iam::ACCOUNT-ID:mfa/SERIAL-NUMBER
Root MFA: arn:aws:iam::ACCOUNT-ID:mfa/root-account-mfa-device